Ijlal Loutfi
on 10 April 2026
Ubuntu 26.04 LTS is one of our most securely-designed LTS releases. Instead of just adding features, Ubuntu 26.04 LTS got stronger everywhere at once, by raising the security floor across every layer of the system simultaneously – and it did so without breaking deployments or demanding manual intervention. By focusing on the heart of security, the defaults , we were able to reinforce Ubuntu’s security in new ways. In this article, we’ll walk you through what’s new in security for Ubuntu 26.04 LTS, including:
- Hardware-backed encryption that’s genuinely production-ready
- Cryptographic defaults that are post-quantum aware
- Enterprise grade support for all leading confidential computing technologies on both the guest and host sides
- Web servers that reject legacy TLS
- Continued effort to “oxidise” security-sensitive parts and making memory-safe implementations of rust-coreutils and sudo-rs the default.
- Identity services that refuse to run as root
- Firmware and secure boot hardened end to end
- A control plane that makes all of it visible, manageable, and auditable long after deployment
Ubuntu 26.04 LTS sets a materially higher default security floor for the next decade of Linux deployments across desktops, servers, confidential VMs, cloud images, and edge systems. For organizations standardizing on Ubuntu as a secure foundation, this is the release they will want to build on.
Security is no longer installer-time only: Security Center becomes a control plane
Historically, key security decisions (such as disk encryption or secure boot posture) were made at installation and rarely revisited. Ubuntu 26.04 LTS changes that.
The Security Center now surfaces critical platform protections in a way that makes them inspectable and manageable after deployment. Administrators can review and manage:
- TPM-backed Full Disk Encryption state
- Recovery mechanisms
- Secure Boot status
- Disk protection configuration
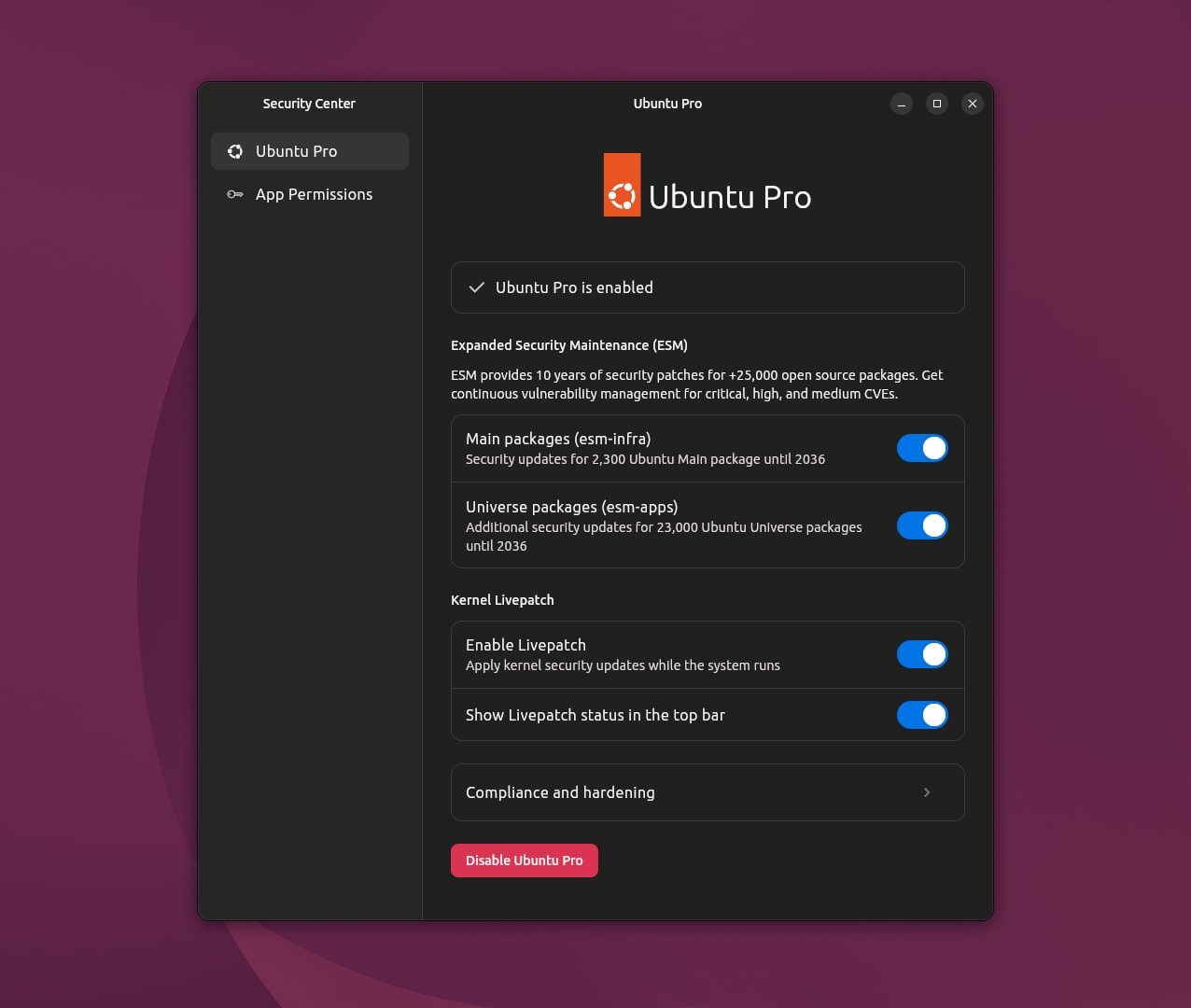
This is a shift in philosophy, where security is not a checkbox during setup. It is a lifecycle responsibility. Ubuntu 26.04 LTS makes that responsibility visible and actionable. For managed desktop fleets and enterprise environments, that reduces blind spots and increases auditability.
TPM-backed Full Disk Encryption is ready for real-world deployment
TPM-backed FDE enters general availability with Ubuntu 26.04 LTS. We had already introduced this capability in earlier releases, behind an experimental flag, and with Ubuntu 26.04 LTS, we are making it operationally robust and enterprise ready. The work in this release focuses on the failure modes that matter in production:
- Recovery-key handling during firmware updates is predictable and surfaced before a potentially breaking reboot
- Known incompatibilities, such as Absolute/Computrace, are explicitly documented and must be accounted for
- Kernel module requirements for certain storage configurations are clearly defined
This is what production readiness looks like: fewer undefined states, fewer surprises during updates, and clearer hardware boundaries. With this, hardware-anchored encryption is no longer experimental; On Ubuntu 26.04 LTS, it is a first-class security mechanism.
Confidential computing: host and guest support for SEV-SNP and TDX
Ubuntu 26.04 LTS ships fully integrated host and guest support for both AMD SEV-SNP and Intel TDX, the two technologies defining the future of confidential cloud infrastructure.
This is a capability with great potential, as it means you can now run virtual machines whose memory is encrypted and integrity-protected by the CPU itself.
Other distributions offer only pieces of this. In contrast, Ubuntu 26.04 LTS delivers the full stack: kernel, firmware, and tooling, integrated and ready to deploy. For public cloud providers, regulated industries, AI workloads, and anyone serious about data sovereignty, Ubuntu offers a comprehensive platform for confidential computing.
Strengthening the security core with memory-safe foundations
Ubuntu 26.04 LTS continues Canonical’s deliberate effort to strengthen the system by “oxidising” security-sensitive components, replacing legacy implementations with memory-safe alternatives written in Rust where they are sufficiently mature. This transition follows a staged approach, with key tools first validated in interim releases before being promoted into the LTS once they meet strict readiness criteria.
In this release, rust-coreutils provides the system’s core utilities and sudo-rs becomes the default sudo implementation, while the traditional GNU coreutils and original sudo remain available for compatibility and fallback.
Modern cryptography by default
Ubuntu 26.04 LTS ships OpenSSH 10.2 and continues the deliberate removal of legacy cryptography, alongside updates to the broader system cryptography stack (including OpenSSL).
Key changes include:
- Hybrid post-quantum key exchange (mlkem768x25519-sha256) available by default
- Complete removal of DSA support
- DSA host keys are no longer generated
- The SSH server no longer reads ~/.pam_environment, reducing environment injection risks
There is no migration toggle required to benefit from modern key exchange. Instead, these features are now default.
Identity and directory services run with less privilege
Some of the most meaningful security changes in Ubuntu 26.04 LTS are not visible in screenshots, they are visible in process tables.
- SSSD now runs as the dedicated sssd user instead of root
- OpenLDAP runs in AppArmor enforce mode
- Password hashing configuration in OpenLDAP is improved with tunable PBKDF2 iteration control
In addition, Ubuntu 26.04 LTS introduces authd as a supported authentication framework, enabling integration with cloud identity providers using modern standards such as OpenID Connect.
This allows Ubuntu systems, across both Desktop and Server, to adopt modern authentication methods, including multi-factor authentication (MFA) and conditional access policies, aligned with enterprise identity platforms.
Identity services are high-value targets. Running them with reduced privilege and enforced confinement meaningfully reduces blast radius in the event of compromise.Get Add-ons
Secure Boot and firmware hardening
Ubuntu 26.04 LTS updates firmware components and tightens Secure Boot posture:
- NX (No-Execute) is enabled across Secure Boot variants
- Legacy strictnx variant removed in favour of consolidated hardened builds
- OVMF firmware packages are aligned to virtualization security technologies such as AMD SEV and Intel TDX
Boot integrity is foundational. Hardening at this layer strengthens the chain of trust from firmware to user space.
Web and TLS defaults move forward
Ubuntu 26.04 LTS updates its core web stack while continuing the distribution’s long-running move away from legacy TLS. It ships with Apache 2.4.66 and Nginx 1.28.2, and aligns their packaged defaults with modern security standards: Apache disables TLS 1.0 and 1.1 by default, and Nginx defaults to TLS 1.2 and TLS 1.3.
This change builds on the TLS hardening introduced in previous LTS releases, ensuring that both the underlying crypto libraries and out-of-the-box web server configurations consistently follow RFC 8996, which deprecated TLS 1.0 and 1.1.
A modern kernel and container baseline
Ubuntu 26.04 LTS aligns with a modern upstream Linux kernel baseline 7.0 and the latest container runtimes. Security-relevant changes include:
- Strengthened cgroup mount options (nsdelegate, memory_recursiveprot, memory_hugetlb_accounting)
- Updated container stack:
- containerd 2.2.1
- runc 1.4.0
- docker.io 29 with nftables backend support and containerd image store defaults
This ensures that isolation semantics and container boundaries are built on a contemporary substrate. This is especially important for cloud-native workloads.
Evolving application confinement with AppArmor
Ubuntu continues to strengthen application isolation through ongoing enhancements to AppArmor, the system’s mandatory access control framework. A key area of development is user-facing permission prompting for snapped applications, designed to provide more granular and transparent control over how applications access sensitive system resources such as files, devices, and network interfaces.
By making these access decisions more visible and explicit, AppArmor prompting aims to improve both security and user awareness of application behavior. This capability is available as an experimental feature and is not yet part of the default security posture in Ubuntu 26.04 LTS, reflecting a broader direction towards tighter application sandboxing and more accountable permission models in future Ubuntu releases.
What makes Ubuntu 26.04 LTS strong
Ubuntu LTS releases define the security baseline that enterprises, governments, cloud providers, and device manufacturers build on for years. Ubuntu 26.04 LTS is no different.
Over the past several cycles, Ubuntu has been rearchitecting its security model from the ground up: modernizing cryptography, anchoring trust in hardware, stripping privilege from core services, and moving security out of the installer and into surfaces where it can actually be managed.
With Ubuntu 26.04 LTS, those changes become the new normal. Deploy it with confidence.
